| 1 |
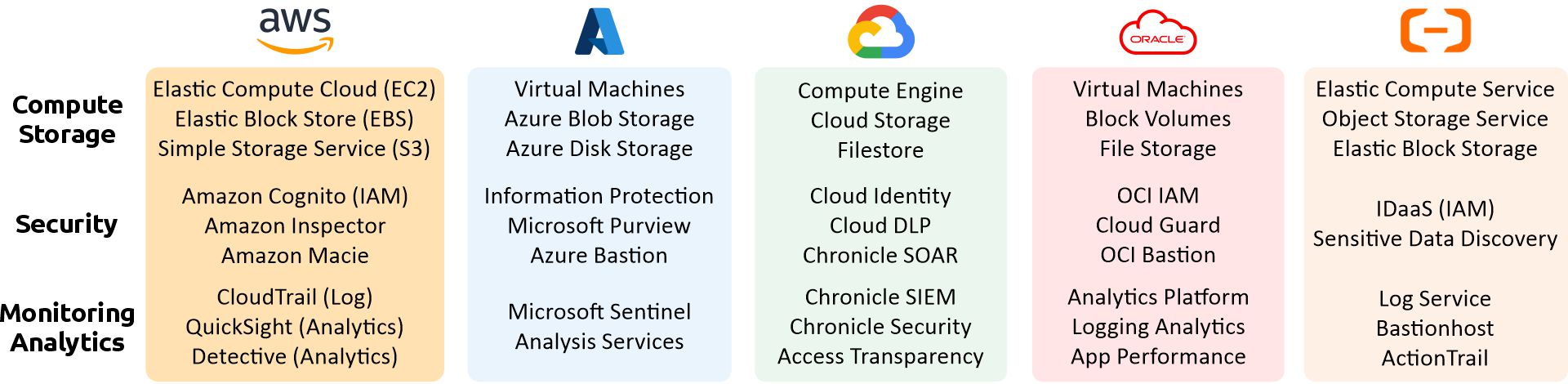
Elastic Compute Cloud (EC2) |
Amazon |
Compute |
Cloud |
|
https://aws.amazon.com/ec2/ |
| 2 |
Elastic Block Store (EBS) |
Amazon |
Storage |
Cloud |
|
https://aws.amazon.com/ebs/ |
| 3 |
Simple Storage Service (S3) |
Amazon |
Storage |
Cloud |
|
https://aws.amazon.com/s3/ |
| 4 |
Amazon Cognito |
Amazon |
IAM |
Cloud |
|
https://aws.amazon.com/cognito/ |
| 5 |
Amazon Inspector |
Amazon |
Vulnerability Management |
Cloud |
|
https://aws.amazon.com/inspector/ |
| 6 |
Amazon Macie |
Amazon |
Data Security |
Cloud |
|
https://aws.amazon.com/macie/ |
| 7 |
AWS Key Management Service |
Amazon |
KMS |
Cloud |
|
https://aws.amazon.com/kms/ |
| 8 |
AWS CloudHSM |
Amazon |
KMS |
Cloud |
|
https://aws.amazon.com/cloudhsm/ |
| 9 |
AWS CloudTrail |
Amazon |
Logging |
Cloud |
|
https://aws.amazon.com/cloudtrail/ |
| 10 |
Amazon QuickSight |
Amazon |
Analytics |
Cloud |
|
https://aws.amazon.com/quicksight/ |
| 11 |
Amazon Detective |
Amazon |
Analytics |
Cloud |
|
https://aws.amazon.com/detective/ |
| 12 |
AWS Artifact |
Amazon |
Reports |
Cloud |
|
https://aws.amazon.com/artifact/ |
| 13 |
Azure Virtual Machines |
Microsoft |
Compute |
Cloud |
|
https://azure.microsoft.com/en-us/products/virtual-machines/ |
| 14 |
Azure Blob Storage |
Microsoft |
Storage |
Cloud |
|
https://azure.microsoft.com/en-us/products/storage/blobs/ |
| 15 |
Azure Disk Storage |
Microsoft |
Storage |
Cloud |
|
https://azure.microsoft.com/en-us/products/storage/disks/ |
| 16 |
Microsoft Sentinel |
Microsoft |
SIEM |
Cloud |
|
https://azure.microsoft.com/en-us/services/microsoft-sentinel/ |
| 17 |
Microsoft Purview |
Microsoft |
Data Security |
Cloud |
|
https://azure.microsoft.com/en-us/products/purview/ |
| 18 |
Azure Information Protection |
Microsoft |
Data Security |
Cloud |
|
https://azure.microsoft.com/en-us/services/information-protection/ |
| 19 |
Azure Bastion |
Microsoft |
Network |
Cloud |
|
https://azure.microsoft.com/en-us/services/azure-bastion/ |
| 20 |
Key Vault |
Microsoft |
KMS |
Cloud |
|
https://azure.microsoft.com/en-us/products/key-vault/ |
| 21 |
Azure Dedicated HSM |
Microsoft |
KMS |
Cloud |
|
https://azure.microsoft.com/en-us/services/azure-dedicated-hsm/ |
| 22 |
Compute Engine |
Google |
Compute |
Cloud |
|
https://cloud.google.com/compute |
| 23 |
Cloud Storage |
Google |
Storage |
Cloud |
|
https://cloud.google.com/storage |
| 24 |
Filestore |
Google |
Storage |
Cloud |
|
https://cloud.google.com/filestore |
| 25 |
Cloud Identity |
Google |
IAM |
Cloud |
|
https://cloud.google.com/identity |
| 26 |
Cloud Data Loss Prevention |
Google |
Data Security |
Cloud |
|
https://cloud.google.com/dlp |
| 27 |
Chronicle SOAR |
Google |
Vulnerability Management |
Cloud |
|
https://cloud.google.com/solutions/security-orchestration-automation-response |
| 28 |
Secret Manager |
Google |
KMS |
Cloud |
|
https://cloud.google.com/secret-manager |
| 29 |
Titan Security Key |
Google |
IAM |
Cloud |
|
https://cloud.google.com/titan-security-key |
| 30 |
Chronicle SIEM |
Google |
SIEM |
Cloud |
|
https://cloud.google.com/solutions/security-information-event-management |
| 31 |
Chronicle Security Operations |
Google |
Vulnerability Management |
Cloud |
|
https://cloud.google.com/solutions/chronicle-security-operations |
| 32 |
Access Transparency |
Google |
Logging |
Cloud |
|
https://cloud.google.com/access-transparency |
| 33 |
Oracle Virtual Machines |
Oracle |
Compute |
Cloud |
|
https://www.oracle.com/cloud/compute/virtual-machines/ |
| 34 |
Block Volumes |
Oracle |
Storage |
Cloud |
|
https://www.oracle.com/cloud/storage/block-volumes/ |
| 35 |
Object Storage |
Oracle |
Storage |
Cloud |
|
https://www.oracle.com/cloud/storage/object-storage/ |
| 36 |
File Storage |
Oracle |
Storage |
Cloud |
|
https://www.oracle.com/cloud/storage/file-storage/ |
| 37 |
Identity and Access Management |
Oracle |
IAM |
Cloud |
|
https://www.oracle.com/security/cloud-security/identity-cloud/ |
| 38 |
Cloud Guard |
Oracle |
Analytics |
Cloud |
|
https://www.oracle.com/security/cloud-security/cloud-guard/faq/ |
| 39 |
Bastion |
Oracle |
Network |
Cloud |
|
https://www.oracle.com/security/cloud-security/bastion/ |
| 40 |
Data Safe |
Oracle |
Data Security |
Cloud |
|
https://www.oracle.com/security/database-security/data-safe/ |
| 41 |
Vulnerability Scanning |
Oracle |
Vulnerability Management |
Cloud |
|
https://www.oracle.com/security/cloud-security/vulnerability-scanning-service/ |
| 42 |
Key Management |
Oracle |
KMS |
Cloud |
|
https://www.oracle.com/security/cloud-security/key-management/ |
| 43 |
Oracle Analytics Platform |
Oracle |
Analytics |
Cloud |
|
https://www.oracle.com/business-analytics/analytics-platform/ |
| 44 |
Logging Analytics |
Oracle |
Analytics |
Cloud |
|
https://www.oracle.com/manageability/logging-analytics/ |
| 45 |
Elastic Compute Service |
Alibaba |
Compute |
Cloud |
|
https://www.alibabacloud.com/id/product/ecs |
| 46 |
Elastic Block Storage |
Alibaba |
Storage |
Cloud |
|
https://www.alibabacloud.com/product/disk |
| 47 |
Object Storage Service |
Alibaba |
Storage |
Cloud |
|
https://www.alibabacloud.com/product/oss |
| 48 |
IDaaS |
Alibaba |
IAM |
Cloud |
|
https://www.alibabacloud.com/product/identity-as-a-service-idaas |
| 49 |
Sensitive Data Discovery & Protection |
Alibaba |
Data Security |
Cloud |
|
https://www.alibabacloud.com/product/sddp |
| 50 |
Log Service |
Alibaba |
Logging |
Cloud |
|
https://www.alibabacloud.com/product/log-service |